Even a Lightning Rod Can’t Do This
… by Gordon Duff, Senior Editor

There is a “magic software” adapted by the US military and “others” called “Planitir.” Long before that, search software called PROMIS had been developed.
The issue is pattern recognition, whether rocket engines seen from a satellite, hidden tanks, underground tunnels or a rash of shootings with a purpose.
There have always been crazy people around, serial killers, terrorists, “mad bombers” and fiends.
However, let’s make a few things clear. In order to stay on task, I have given myself 15 minutes to write this, no more. If I can’t make my point in the equivalent of a short verbal discussion, I have no point. Here we go:
Berwick or Breivik in Norway, children of a political group opposed to Israel. Police have no helicopters, can’t get boats, drive 5mph though news helicopters are overhead and private boaters are saving people while police stand by.
The shooter, in Europe, the land of “no guns,” travels in and out of Poland for military training, is known by police, tied to their Freemason club, a police organization across Europe.
And his bombing, identified as a micro-nuke by experts and his crime, impossible without full police cooperation, has sunk into obscurity.
Take the clock back to Oklahoma City. We have a Ryder van filled with “medium explosive” slurry, low power, open area but it obliterates structural steel, is directional and several other suspects, very probably FBI or related, disappear.
Tim McVeigh’s military career, tending toward “Ranger” or “Special Forces” is erased and we are told to ignore that the FBI who worked in the office all called in sick that day.
![Hasan_nidal[1]](https://www.veteranstodayarchives.com/wp-content/uploads/2012/07/Hasan_nidal1-e1343092414516.jpg)
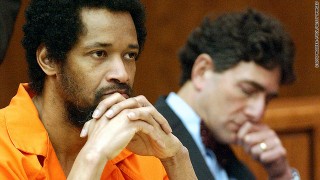
His last station was Walter Reed where he was part of a Bush administration group that was tasked with helping Republican contractors keep control after Democrats got into office.
This put him in high level meetings with Washington’s elite, the big name insiders, he could have killed at any time.
In fact, why was he there at all? Where is he now? Has any journalist looked into the endless number of inconsistencies here, some brought up by the commanding general of Ft. Hood himself, privately, until he was silenced.
A couple of years before, between 6 and 9 hydrogen bombs were stolen from Minot Air Base and flown outside the US only to be turned around and forced down at Barksdale AFB, Louisiana.
The reason for the “transfer” was that Barksdale was informally borrowing enough megatonnage to destroy half the planet based on a “coin flip” between commanders, all outside regulations, national law, military policy and oaths sworn.
In reality, this was an attempt to stage an attack in order to begin a war and begin a military dictatorship under the rule of an obscure religious group formed at the Air Force Academy in Colorado Springs. Twelve involved died mysteriously. Good.
The Air Force lost all its “nuclear rights” and the Secretary of Defense removed them from any nuclear command protocols, essentially making them civilians.
Check on this, the Air Force is now basically an untrusted civilian flying club.
Remember the DC sniper? He did 16 years in Special Forces, sniper school, karate expert, much more. There is no record of him ever leaving the military.
His helper had been picked up as an illegal alien but released INSIDE the US rather than expelled. That is illegal.
Williams was never a real Muslim, wore Armani jackets, traveled first class, stayed in homeless shelters and spent money like an Arab prince. No journalist ever asked any of this.
Then I look back at Columbine and ask about it. Why did police wait outside the building until all were dead and firing had stopped for 20 minutes?
Then I think of the shooting last year of Congresswoman Gabby Giffords. She was shot, along with the others killed, including a Federal Judge who should have had two armed marshals with him, by someone who had undergone three years of Army “entry preparations” that included meetings with military psychiatrists.
There should have been a dozen police on site but, instead, no one showed up for over 40 minutes though the nearest police car was 1 minute away.
This can be proven in seconds.
The last shooting, the “Batman” killings, where will this lead? What will we learn?
If I add the oddities of 9/11 I will go over time but they are “off the scale.”
CONCLUSION
It is my belief that military software has to recognize this, the anthrax poisonings, other events we miss, the patterns of attacks across Africa and elsewhere.
They see the hand of an organization tasked with building fear and distrust, government, personal safety, dependence, disenfranchisement.
Add rigged elections to this like Scalia brags about whenever he gets near a camera and more pattern emerges.
All this data is subjected to military software and I know for certain that they have these conclusions, know the culprits but may actually also know they may be an integral part of the problem themselves.
Think of the 12 year wars.
Time to stop. I had 9 minutes to make a point.
Editing: Jim W. Dean
Gordon Duff posted articles on VT from 2008 to 2022. He is a Marine combat veteran of the Vietnam War. A disabled veteran, he worked on veterans and POW issues for decades.
Gordon is an accredited diplomat and is generally accepted as one of the top global intelligence specialists. He manages the world’s largest private intelligence organization and regularly consults with governments challenged by security issues.
Duff has traveled extensively, is published around the world, and is a regular guest on TV and radio in more than “several” countries. He is also a trained chef, wine enthusiast, avid motorcyclist, and gunsmith specializing in historical weapons and restoration. Business experience and interests are in energy and defense technology.
ATTENTION READERS
We See The World From All Sides and Want YOU To Be Fully InformedIn fact, intentional disinformation is a disgraceful scourge in media today. So to assuage any possible errant incorrect information posted herein, we strongly encourage you to seek corroboration from other non-VT sources before forming an educated opinion.
About VT - Policies & Disclosures - Comment Policy