DID CIA KILLER “BRIBED” OUT OF PAKISTAN JAIL HEAD “TEAM BIN LADEN?”
DAVIS RELEASE “MATTER OF HIGHEST NATIONAL SECURITY

By Gordon Duff STAFF WRITER/Senior Editor
————————————-
“.. to blackmail Pakistan into appointing a new intelligence chief willing to ‘take orders’ from Washington.”
————————————–
Sources tell us that the “lifelines” that kept what has been identified as Osama bin Laden safe inside Pakistan were operated under the supervision of CIA operative Raymond Davis. There were two safehouses in Abbottabad, one for “bin Laden,” the other for the CIA. We are told that this explains why there was no Al Qaeda security detail. The CIA was in charge of that.
Davis, arrested in Lahore earlier in the year, faced trial for murder until released because of cash payments made to the families of the victims. Davis led a super-secret CIA team thought initially by Pakistan to be coordinating Taliban and Indian terror networks. It is now reported that he was the handler for “the man from Abbottabad,” the man America claims was Osama bin Laden.
[youtube eIztqcTsJ7U]
Reports indicate that Osama bin Laden wasn’t captured for a good reason. The individual identified as Osama bin Laden was a replacement used in video and audio terror threats that have failed analysis and been debunked as counterfeit.

Documents identified by former FBI translator Sibel Edmonds and former Undersecretary of State Steve Pieczenik, a physician, clearly identify bin Laden as associated with the CIA long after he was identified as the leader of the shadowy Al Qaeda network. Pieczenik also confirms that bin Laden was fatally ill long ago. Multiple confirmations in Pakistan and the US have bin Laden dying in 2001, not long after he issued a categorical denial of complicity in 9/11.
IT’S BIN LADEN’S BIRTH CERTIFICATE WE REALLY NEED

Not long after bin Laden’s reported death, several “clones” appeared including one matching the appearance of the “bin Laden” who appears in videos captured in Abbottabad. It is not certain whether this “bin Laden” or a subsequent clone was the individual who may have been killed in the recent US operation.

One thing for sure, it was not the long dead CIA financier, Osama bin Laden.
Sources report that the recent “bin Laden” operation was in retaliation for Pakistan’s arrest of bin Laden handler, Raymond Davis. Other reasons with limited or unreliable confirmations claim the US wishes to blackmail Pakistan into appointing a new intelligence chief willing to “take orders” from Washington.
Reliable reports from within the US intelligence community state that a major factor in the timing of the recent operation was tied to the “musical chairs” in Washington with Leon Panetta leaving the CIA to take over as Secretary of Defense upon the retirement of Robert Gates and the General Petraeus’ move to take over the CIA.
The killing of “bin Laden,” real or a “clone” under Panetta’s watch would prevent General Petraeus from becoming “unmanageable” were he able to make the same claim. Petraeus is cited for having presidential aspirations and the CIA directorship has been a stepping stone to the White House before as seen with George H.W. Bush.
OPERATIONAL INCONSISTENCIES
The Navy Seal operation attributed to the assassination of Osama bin Laden as reported to the world is a hollow fiction. We are not here to discuss the legal merits, the questions of who or why but rather how.
There were two main areas of concern with the initial cover story of the killing of Osama bin Laden. The first, of course, were the contradictions, guns, then no guns,shooting then no shooting and the lack of evidence of this being an assault on a “high value” terrorist target. DEA (Drug Enforcement Agency) assaults on “wrong houses,” something too common in the United States, assaults that often accidentally target innocent senior citizens or homes with small children, leave more convincing evidence than the attack on what Colin Powell has called “the worst person on earth.
The second issue is the confirmations received of what was reported all along. Osama bin Laden had been dead for a decade. Confirmations received from the highest sources in the US intelligence community confirm that Osama bin Laden’s body was recovered by Special Forces operating in Afghanistan in December 2001. His body was frozen and kept in storage for a date when it would be of advantage to the United States to use it for maximum advantage.
Another reason for the decision to “thaw and assassinate” was to deliver a knockout punch to Republican presidential contenders, in particular Donald Trump, already reeling from the “birth certificate” fiasco.
As this information directly contradicts all of the varied stories released by the White House thus far, one could safely assume that no information offered, not that through official channels, a mishmash of contradiction and absurdity nor that offered here, reeking of conspiracy and sinister intent, can safely be relied upon.
In fact, there is no competent analysis of any kind in the mainstream press and, though much of the work in the alternative media may ring of truth or seem more logical, it also has an aspect of conjecture to it with some exceptions. There is a wealth of authoritative opinion regarding the death of bin Laden in 2001, two Pakistani prime ministers, Bhutto and Musharraf, their top intelligence officer at the time, General Hamid Gul, currently editor at VT, and a wealth of senior US officials. These issues may be followed in the media and a reader may choose which “reality” to accept. There is no sadder state of affairs than for such uncertainty to exist involving key areas of national security.
REAL OPERATIONS IN A REAL WORLD
An operation as reported, one planned and executed by the Joint Special Operations Command, the organization tasked with carrying out extrajudicial executive actions such as this one makes use of all the resources the United States has at its disposal. We will discuss some of those resources and how they would have been tasked in an effort such as the one described.
Most intelligence operations begin with some sort of intercept, a phone call or computer email. There are more acronyms than you can shake a stick at tied to intelligence. Acronyms serve one purpose, to attempt to mislead and astound while either making excuses for failures or inventing nonexistent successes, all the while spending taxpayer funds like a drunken sailor in a cathouse. SIGINT or COMINT or COMPINT or ELINT or IMAGINT, it’s all baloney, smoke and mirrors.
Funniest of all is HUMINT. This means “human intelligence” or “some guy told me….”
The Abbottabad operation would have begun with an intercept of a recognized and attributed voice print, a form of biometics or an email that said a bit too much. It could have been HUMINT, someone saw something or, as is usually the case, saddly, it is more likely IMAGINARINT, or imaginary intelligence. This is information that people simply invent. Most intelligence is IMAGINARINT.
A ten year manhunt for a deadman who has been in a freezer in Bahrain, an arch-criminal used as a catchall boogeyman needs alot of IMAGINARINT and the JSOC, Dick Cheney’s “red-headed stepchild,” is the type of organization for just such an occasion. They are at their best when stopping imaginary attacks or tracking imaginary terror cells. In order to provide HUMINT to back up their IMAGINARINT, they kidnap and torture the odd cook or cab driver, sometimes for years on end, until they are able to force their victims to agree with anything they say.
Then the victim is put on trial, convicted and imprisoned for life as a reward.
SATELLITES
The US has advanced optical satellites which can be tasked for surveillance but the most effective “first look” at the compound in Abbottabad would have been through ultra-high resolution synthetic aperture radar (SAR) imagery. This would have seen through the buildings and beneath, locating any tunnels which might have been built for egress. It also would have identified vehicles, room layouts, weapons caches and even the location of furniture.
EYES ON THE GROUND
The next step would have been to place “eyes on the ground,” in this case, teams of CIA private contractors who would maintain 24 hour a day surveillance of the compound. Commonly, they would have equipment to monitor or, if need be, jam communications within a square kilometre. They would be able to intercept text messages and decrypt any wifi communication. They would have become the defacto gateway, the service provider for any communication. All phone, text, or computer communication would have passed through them and even been altered in the process.
[youtube zxoAQ-A4XBg]
Satellite telephones are quite vulnerable also.
The standard kit, which includes the two large “briefcase” modules would also be supplemented with a variety of other “tricks.”
THERMAL IMAGERY
The site would be under constant thermography scanning. Through the walls, personnel, electrical systems, generators and cooking devices would be quickly located. Patterns of movement would be established.
TAGGING
Anyone leaving the compound would be “tagged” using specialized chemical agents or nano-electronics. This could be done passively through door handles or by seeding the dust on the stairs. More likely, however, “innocent passersby” would aid in this process. Within days, every person in the compound would be either actively or passively “tagged” along with anyone outside the compound that came in contact with them. Eventually, everyone with personal contact would be identified and subject to a cascade of surveillance, signals – phone, computer, etc, and more.
ACOUSTIC
Decades ago, laser systems were developed that were could produce modulations, such as voice, by focusing on reflective surfaces. The range of these is endless but window film was developed to defeat this technology. Now, microelectronics allow undetectable sensors, even resembling small stones, to be attached or dropped anywhere, including areas with no access at all. Long long ago, SWAT teams began using microphone/transmitter couplings fired by sling shots using an exclusive hi-tech contact adhesive, tar and axle grease.
You could shoot one onto a window or other surface and, in an instant, you were “bugging” a room. Current technologies are decades beyond this with nano-technologies being tested and possibly used that simulate insects.
SMILE, YOU’RE ON CANDID CAMERA
Yes, the insect UAV (unmanned aerial vehicle) may exist and may be operational. Movies have featured such things for many years and tests of small UAV aircraft are a big hit on www.youtube.com. Commonly used UAVs resemble small
birds. Recent advances even allow such vehicles to mimic the flight of birds themselves. Sensor arrays allow high resolution video surveillance and limited thermal capability. Years ago, units that fit in a backpack were common, deployed with Marines. Things have gone far beyond this.
BIOMETRICS
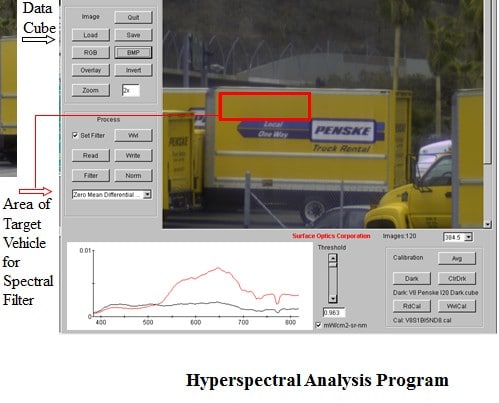
The science of biometrics can mean something as simple as palm geometry, voice recognition, retina scan or fingerprint identification. Facial recognition is used everywhere and huge databases are being developed based on the use of this technology at airports, train stations , border checkpoints and other less obvious areas. There are more intrusive technologies at use, however. One of these is called “hyperspatial analysis.” This is a list of some of the capabilities of such a system currently deployed.
- Facial recognition. Provides the unique ability to conduct real time analysis of biometric facial features and match those features to a data base of known persons of interest. Once identified, the standard beehive features allows real time tracking of the person or persons within the xxx network.
- Audio detection. Permits the xxxxxx to identify and provide the exact source and location of selected sounds, such as a weapons discharge or explosion within the xxxxxxxx network. System will provide GPS coordinates and or standard military mapping coordinates.
- Thermal imaging. Provides state-of-the-art thermal imaging for enhanced detection and anti-terrorism capabilities. This feature is a critical component in the identification of concealed personnel, bio hazards, and heat generating threats such as recently used weapons, some explosive compounds, etc.
- Air sampling. Provides real time detection of selected hazardous gases. This feature is a critical component for effective chemical or biological threat detection.
- Radiological detection. Provides real time detection and tracking of sources of radiation within the xxxxxx network. Designed to provide coverage at ranges up to 50 meters.
- Concealed trace detection. Real time detection and identification of up to 120 different hazardous substances at distances of up to 100 feet, underneath standard clothing items.
- Long- range trace detection. Real time detection and identification of over 100 different hazardous substances, including explosives, at distances of up to 5 kilometers
A typical clandestine deployment of a hyperspatial array would be on a refrigeration truck, delivering meat or produce. The unit would be housed in the cooling unit. Such a unit was undoubtedly used in this operation which would have identified anyone entering or leaving the compound along with the presence of any weapons or explosives.
BIO-CHEM AIDES IN SURVEILLANCE
A typical ploy in such a case is to introduce a biological or chemical agent to the air, water or food. Within hours, even minutes, individuals would show symptoms of a number of common diseases, fatal if desired but for use of surveillance, requiring medical care entailed by measured application of moderate to severe “discomfort.”
This allows for, not only medical personnel to be questioned but for a general deterioration in awareness and capability as members of the household are incapacitated. Generally, in such cases, there is a need to “reach out” which, while COMINT protocols are in place, will lead to an expanded list of suspects.
At any point, undetectable chemical incapacitating agents could have been administered in order to gain entry. The most effective are synthetic opiates that work almost immediately.
S.O.P
All capabilities listed here and many more not discussed were available for use in Abbottabad. All equipment was not just in theatre but inside Pakistan.
Given the long advanced warning and the importance given to the target, several technologies not listed here were likely to be used as well. What is clear and what we can easily surmise is that, due to the capabilities outlined and the poor security of the Abbottabad compound, the movements and identity and location of anyone inside would have been known.
If anything can be believed of what we have been told, at best there was very light opposition and a 20 plus man force, highly trained, fully armoured from head to foot could have easily accomplished the capture of their target without, not only using lethal force but without being armed at all.
Considering the training and ability of Navy Seals, a 3 man team might have been 2 too many.
[youtube _q7rSC0Da0c]
ATTENTION READERS
We See The World From All Sides and Want YOU To Be Fully InformedIn fact, intentional disinformation is a disgraceful scourge in media today. So to assuage any possible errant incorrect information posted herein, we strongly encourage you to seek corroboration from other non-VT sources before forming an educated opinion.
About VT - Policies & Disclosures - Comment Policy



